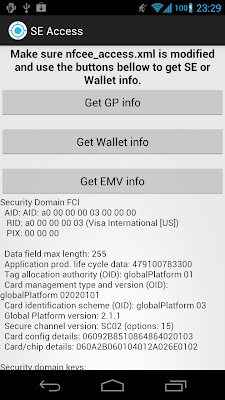
Exploring Google Wallet using the secure element interface

In the first post of this series we showed how to use the embedded secure element interface Android 4.x offers. Next , we used some GlobalPlatform commands to find out more about the SE execution environment in the Galaxy Nexus. We also showed that there is currently no way for third parties to install applets on the SE. Since installing our own applets is not an option, we will now find some pre-installed applets to explore. Currently the only generally available Android application that is known to install applets on the SE is Google's own Google Wallet . In this last post, we'll say a few words about how it works and then try to find out what publicly available information its applets host. Google Wallet and the SE To quote the Google Play description, 'Google Wallet holds your credit and debit cards, offers, and rewards cards'. How does it do this in practice though? The short answer: it's slightly complicated. The longer answer: only Google knows all the ...